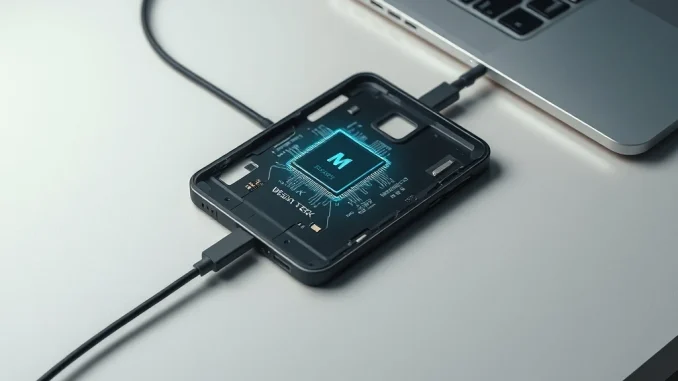
TAIPEI, TAIWAN — January 5, 2026: Semiconductor giant MediaTek has urgently patched a severe security vulnerability in its smartphone chipsets that enabled attackers to steal cryptocurrency wallet seed phrases in under a minute. The critical flaw, discovered by Ledger’s elite white-hat security team, Donjon, exploited a weakness in MediaTek’s secure boot chain. Attackers could compromise affected Android devices using only a USB cable and specialized software, bypassing all operating system security without even booting the phone. The patch, released on January 5th, addresses a threat that security experts warn could have impacted millions of cryptocurrency users globally, highlighting fundamental architectural risks in general-purpose mobile hardware.
MediaTek Secure Boot Chain Vulnerability Explained
Ledger’s Donjon team identified the flaw within MediaTek’s secure boot mechanism, a foundational security layer designed to ensure a device starts only with authorized, verified software. Charles Guillemet, Ledger’s Chief Technology Officer, explained to Cointelegraph that the vulnerability created a bypass. Consequently, an attacker with physical access could connect a powered-off phone to a computer via USB and directly attack the chip’s trusted execution environment. This method completely circumvented Android’s software defenses. The team tested the exploit on a Nothing CMF Phone 1, demonstrating a full compromise in approximately 45 seconds. During that brief window, the attack automatically recovered the device’s PIN, decrypted its storage, and extracted seed phrases from popular software wallets including Trust Wallet, Base, and Phantom.
MediaTek, a leading supplier for mid-range and budget Android devices, collaborated with Ledger on a responsible disclosure process. The chipmaker developed and distributed the necessary firmware patch to device manufacturers in early January. However, security updates require end-user installation. Therefore, millions of phones may remain vulnerable if users delay or ignore security patch notifications. This incident underscores the complex update chain in the Android ecosystem, where chipmakers, OEMs, and carriers all play a role in delivering critical fixes to consumers.
Quantifying the Risk: A Quarter of Android Phones Potentially Affected
The technical exploit specifically targeted devices using a combination of MediaTek processors and the Trustonic Trusted Execution Environment (TEE). Industry analysts estimate this combination powers roughly 25% of the global Android market. With nearly 36 million people managing digital assets on mobile devices as of early 2025, according to Ledger’s market data, the potential attack surface was significant. A single successful exploit could lead to irreversible financial loss, as seed phrases grant complete control over associated cryptocurrency assets.
- Direct Financial Theft: Extracted seed phrases allow attackers to drain wallets instantly, with little recourse for recovery due to cryptocurrency’s irreversible transaction nature.
- Erosion of Mobile Trust: The flaw shakes user confidence in smartphones as secure vessels for financial applications, potentially slowing adoption of mobile-first crypto services.
- Supply Chain Security Scrutiny: The vulnerability originated at the silicon level, shifting security scrutiny from software developers to hardware manufacturers and their proprietary firmware.
Expert Analysis: A Fundamental Architectural Weakness
Security architects emphasize that this flaw is symptomatic of a deeper issue. “Smartphones aren’t built for security,” stated Charles Guillemet in a public statement on X. “Even when powered off, user data – including pins & seeds – can be extracted in under a minute.” He contrasted general-purpose chips, optimized for cost and performance, with dedicated Secure Element chips. Secure Elements, like those used in Ledger’s hardware wallets, are designed with physical and logical isolation as a primary goal. They protect secrets even under direct physical attack. Guillemet’s analysis suggests that while software patches can address specific vulnerabilities, the underlying architecture of mainstream smartphones remains ill-suited for high-stakes key protection. This perspective is echoed by independent security researchers who note that TEE implementations have been a repeated target for sophisticated attacks over the past decade.
Hardware vs. Software Security: A Comparative Landscape
The MediaTek incident reignites the debate over the optimal environment for securing cryptographic keys. While convenient, software wallets on general-purpose operating systems inherit the vast attack surface of the device. Hardware wallets, though less convenient for frequent transactions, isolate the critical signing process. The table below outlines key differences relevant to this vulnerability.
| Security Component | General Purpose Smartphone (e.g., MediaTek/Android) | Dedicated Hardware Wallet |
|---|---|---|
| Key Storage | Trusted Execution Environment (TEE) within main chip | Isolated Secure Element (SE) or secure chip |
| Attack Surface | Large (OS, apps, firmware, physical interfaces) | Extremely limited (designed for a single purpose) |
| Physical Attack Resistance | Vulnerable to glitching, probing, and boot chain attacks | Designed to resist physical tampering, often with active shields |
| Update Mechanism | Complex chain (Chipmaker → OEM → Carrier → User) | Direct, controlled firmware updates from manufacturer |
The Road Ahead: Patching, Awareness, and Architectural Shifts
The immediate path forward centers on remediation and user education. MediaTek has stated the patch is available to its partners, and Ledger strongly urges all users to install the latest security updates for their Android devices immediately. Looking further ahead, the industry may see increased demand for smartphones with discrete, certified Secure Elements for users managing significant digital assets. Some manufacturers have already begun exploring this, integrating enterprise-grade security features into consumer devices. Furthermore, this event will likely influence ongoing standards work around mobile device security for financial applications, potentially leading to stricter certification requirements for chips used in devices marketed for cryptocurrency use.
Industry and Community Response: A Call for Transparency
The disclosure has been met with calls for greater transparency in the semiconductor supply chain. Security researchers advocate for more detailed public documentation of secure boot implementations to facilitate independent review. Within the cryptocurrency community, the advice remains consistent: for substantial holdings, use a dedicated hardware wallet. Software wallets on mobile devices are best suited for smaller, “hot wallet” funds convenient for daily transactions. The swift collaboration between Ledger’s Donjon and MediaTek is viewed as a positive model for responsible disclosure, preventing active exploitation before public knowledge could lead to widespread attacks.
Conclusion
The patched MediaTek vulnerability serves as a stark reminder of the persistent threats in the digital asset ecosystem. It underscores that security is a layered endeavor, and the hardware foundation is critical. While the immediate technical flaw is resolved, the underlying architectural tension between convenience and security in consumer devices remains. For cryptocurrency users, the key takeaways are clear: prioritize installing device security updates without delay, understand the limitations of your chosen storage method, and match the security of your wallet to the value of the assets it holds. As mobile devices continue to evolve as financial hubs, pressure will mount on chipmakers and OEMs to redesign hardware with security as a core feature, not an afterthought.
Frequently Asked Questions
Q1: How do I know if my Android phone is vulnerable to this MediaTek flaw?
If your phone uses a MediaTek processor and the Trustonic TEE, and has not received a security patch dated January 5, 2026, or later, it may be vulnerable. Check your device’s security update status in the Settings menu. When in doubt, install all available updates.
Q2: What should I do if I use a software wallet on my Android phone?
First, ensure your phone’s operating system is fully updated. Second, consider moving the majority of your holdings to a dedicated hardware wallet, using the mobile wallet only for funds needed for regular transactions. Never store large amounts in a single software-based hot wallet.
Q3: Has this vulnerability been actively used by attackers in the wild?
According to Ledger and MediaTek, there is no evidence of active exploitation before the patch was released. The flaw was discovered and disclosed through a responsible process by Ledger’s Donjon team, preventing real-world attacks.
Q4: Are iPhones or phones with Qualcomm chips affected by this specific issue?
No. This particular exploit targeted a specific implementation in certain MediaTek chipsets. However, the broader lesson—that smartphones face physical extraction risks—applies to all devices. Different platforms have different attack surfaces and security models.
Q5: What is a secure boot chain, and why is it important?
The secure boot chain is a series of cryptographic checks performed when a device powers on. Each step verifies the next piece of code (from the chip firmware to the OS loader) before executing it. A flaw here can allow malicious code to run with the highest privileges, bypassing all other security.
Q6: How does this discovery affect the average person who doesn’t use cryptocurrency?
While the demonstration focused on crypto seeds, the same exploit could potentially access other sensitive data stored in the device’s TEE, such as biometric templates, device encryption keys, or corporate credentials. It highlights the importance of regular security updates for all phone users.



