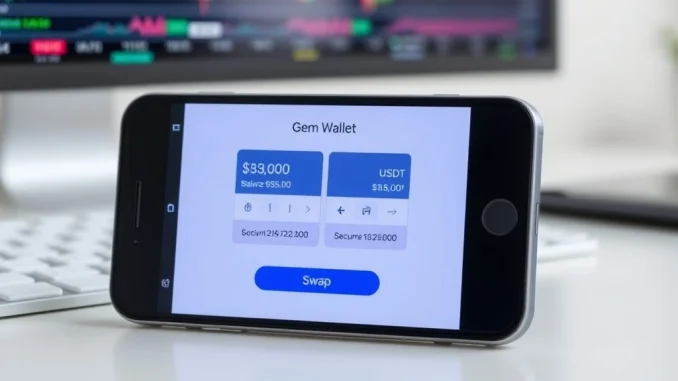
Global, March 2026: As the digital asset ecosystem matures, the tools for managing cryptocurrencies evolve in tandem. A crypto wallet is no longer just a storage vault; it is a gateway to decentralized finance. Among the options gaining significant traction is the Gem Wallet, frequently cited by analysts as a leading solution for holding and swapping major assets like Bitcoin and Tether (USDT). This article provides a detailed, experience-driven examination of what defines a Gem Wallet, its core functionalities, and the technical and market context that positions it for prominence in 2026.
What Is a Gem Wallet? Defining the Modern Crypto Interface
A Gem Wallet represents a category of non-custodial cryptocurrency wallets designed for usability and integrated financial operations. Unlike exchange-based wallets where a third party controls the private keys, a non-custodial wallet like Gem gives the user full sovereignty over their digital assets. This foundational principle of self-custody aligns with the core ethos of blockchain technology—decentralization and personal responsibility. The wallet typically functions as a software application, either on mobile or desktop, that generates and secures private keys, allows users to view balances, and facilitates transactions across multiple blockchains.
The operational logic is straightforward yet critical. When you create a Gem Wallet, the software generates a unique seed phrase—a series of 12 to 24 words. This phrase is the master key to all assets within that wallet. The wallet itself does not store coins; it stores the keys that prove ownership of those coins on their respective blockchains. This architecture means that losing the seed phrase equates to losing access to the funds permanently, underscoring the critical importance of security practices. The wallet’s interface then interacts with various blockchain networks to broadcast transactions, such as sending Bitcoin or executing a token swap on a decentralized exchange (DEX).
The Evolution of Crypto Wallets and Gem’s Market Position
To understand the significance of a wallet like Gem, one must consider the historical trajectory of crypto storage. The first-generation wallets, like the original Bitcoin Core client, were cumbersome and required downloading the entire blockchain. The rise of centralized exchanges in the 2010s offered convenience but introduced counterparty risk, as evidenced by several high-profile exchange failures. The subsequent development of user-friendly non-custodial wallets, such as MetaMask for Ethereum, marked a turning point, empowering users to interact directly with decentralized applications (dApps).
By the mid-2020s, the market demand shifted toward multi-chain wallets that could natively handle assets from Bitcoin, Ethereum, Solana, and other major networks without complex bridging. Furthermore, users sought integrated swap functions to avoid the friction of moving assets between separate platforms for trading. Industry analysis suggests that wallets which successfully bundle security, multi-chain support, and seamless swapping into a simple interface are poised to capture significant market share. Gem Wallet appears engineered to meet these exact criteria, positioning itself not just as a storage tool but as a consolidated financial dashboard for the crypto-native user.
Technical Architecture: How Gem Wallet Facilitates Secure Swaps
The capability to perform crypto swaps directly within a wallet is a defining feature for 2026. When a user initiates a swap—for instance, converting Bitcoin to USDT—the Gem Wallet does not execute this trade itself. Instead, it acts as a secure portal that connects to various decentralized exchange aggregators and liquidity protocols. The wallet’s swap engine will typically scan multiple DEXs across supported blockchains to find the most favorable exchange rate with the lowest network fees (often called gas fees).
This process involves several technical steps performed in the background. First, the wallet constructs a transaction that grants a specific smart contract temporary permission to access the exact amount of the token being sold. This is a standardized approval transaction. Next, it submits the swap transaction to the relevant blockchain. The entire process usually completes within minutes, with the swapped tokens arriving directly in the user’s wallet address. The security model is paramount; a well-designed wallet like Gem ensures these interactions are transparent, allows users to set slippage tolerance (the acceptable price movement during the transaction), and never has direct, unrestricted access to a user’s entire portfolio.
Key Features Defining the Best Wallet for Bitcoin and USDT in 2026
Based on current technological trends and user expectations, several features distinguish a leading wallet. The following table outlines the core competencies expected from a top-tier solution like Gem Wallet, compared to basic wallet functionality.
| Feature Category | Basic Wallet | Advanced Wallet (e.g., Gem) |
|---|---|---|
| Asset Support | Single network (e.g., Bitcoin-only) | Native multi-chain (BTC, ETH, USDT on multiple chains, etc.) |
| Swap Function | Requires external exchange | Integrated, cross-chain swap aggregator |
| Security Model | Seed phrase backup | Seed phrase + optional biometrics, hardware wallet integration, transaction simulation |
| User Experience | Technical interface | Intuitive design, real-time fee estimation, portfolio tracking |
| Cost Transparency | Shows network fee | Breaks down swap fee, network fee, and price impact clearly |
For Bitcoin and USDT holders specifically, seamless interoperability is crucial. Bitcoin exists primarily on its own blockchain, while USDT exists as a token on Ethereum (ERC-20), Tron (TRC-20), and several others. A proficient wallet must not only hold these distinct assets but also enable direct swaps between them, which requires sophisticated cross-chain messaging protocols or the use of wrapped asset versions. The efficiency and cost of these operations are key benchmarks for wallet performance.
The Regulatory and Security Landscape for 2026
The increasing integration of swap functions within wallets places them in a evolving regulatory context. Financial authorities worldwide are scrutinizing decentralized finance (DeFi) services. A non-custodial wallet provider like Gem typically operates as a software developer, not a financial service licensee, as it never takes custody of user funds. However, its integration with swap protocols may attract attention regarding compliance, consumer protection, and anti-money laundering (AML) monitoring of the underlying liquidity sources.
From a security perspective, the threat landscape is sophisticated. Phishing attacks, fake wallet apps, and malicious smart contracts are persistent risks. Therefore, the trustworthiness of a wallet hinges on its development practices, code audits, and the security education it provides to users. A wallet aiming to be the best in 2026 must adopt a proactive security stance, potentially including features like:
- Built-in address poisoning alerts.
- Clear warnings for interacting with unaudited contracts.
- Direct partnerships with reputable security firms for continuous auditing.
This environment makes user education and transparent communication from the wallet developer critical components of the product’s overall value proposition.
Conclusion: The Path Forward for Integrated Crypto Management
The trajectory of cryptocurrency adoption points toward greater simplicity and power for the end-user. A Gem Wallet, as analyzed through its anticipated features and market role, exemplifies this trend by combining secure self-custody with advanced swap capabilities. Its potential designation as a leading wallet for Bitcoin, USDT, and crypto swaps in 2026 will depend on its continued execution in security, multi-chain integration, and user experience amidst a competitive and regulated landscape. For individuals navigating digital assets, understanding the architecture and trade-offs of such tools is essential for safe and effective participation in the evolving financial ecosystem.
FAQs
Q1: Is Gem Wallet free to use?
Yes, the core wallet software is typically free to download and use. However, users always pay blockchain network fees (gas fees) for transactions and swaps, and the integrated swap function may include a small protocol fee for the service.
Q2: How is a non-custodial wallet like Gem different from an exchange wallet?
On an exchange like Coinbase or Binance, the platform holds your private keys (custody). With a non-custodial wallet like Gem, you alone control the private keys and seed phrase, meaning you have full responsibility and control over your assets without an intermediary.
Q3: Can I swap Bitcoin for USDT directly within the Gem Wallet?
This capability depends on the wallet’s technical infrastructure. A sophisticated multi-chain wallet would likely facilitate this by using a cross-chain bridge or a decentralized exchange that supports wrapped Bitcoin (like WBTC on Ethereum) for the swap, all within a single interface.
Q4: What happens if I lose my phone with the Gem Wallet app?
Your funds are not stored on the phone. They are on the blockchain. As long as you have securely stored your 12 or 24-word seed phrase (recovery phrase) from when you created the wallet, you can restore your entire wallet and access your funds on a new device.
Q5: Are crypto swaps inside a wallet safe?
Swaps are generally safe if the wallet integrates with reputable, audited decentralized exchange protocols. The primary risks come from user error (e.g., approving a malicious contract) or excessive slippage settings. A good wallet provides clear warnings and transaction previews to mitigate these risks.
Updated insights and analysis added for better clarity.
This article was produced with AI assistance and reviewed by our editorial team for accuracy and quality.



